Change your Twitter handle but KEEP your followers and links
Sometimes we outgrow our Twitter handles. I did.
At the same time, once we’re established, the thought of losing the possible thousands of followers we’ve already amassed can be quite daunting. Undeterred, I looked into this anyway.
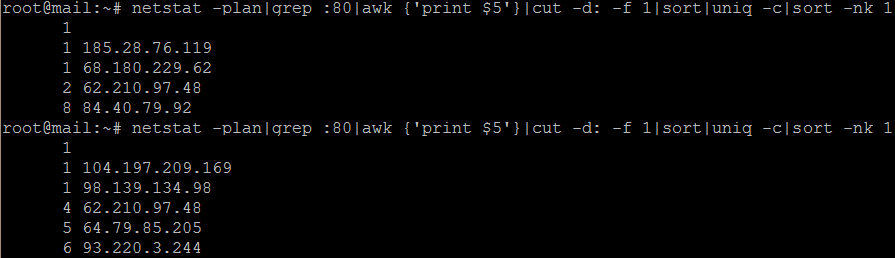
It is actually possible to change your Twitter handle through your account settings in just a few clicks. Take a look at the screenshot below:
This ensures that you keep all your profile data (profile text, images, previous tweets, followers – essentially everything), just with a new name. Brilliant, right?
There’s a catch:
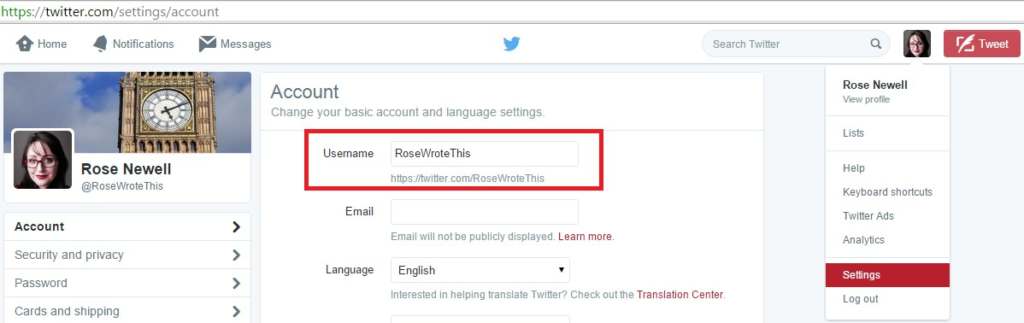
Your old name now becomes free. At best, it turns into a Twitter 404 page. See below:
At worst, some sneaky or malicious character can spot the existing link juice pointing to your old username and that it has now become available. They can use this to spam your followers or even impersonate you, damaging your image and potentially scamming your friends.
On top of that, you lose all the link juice you already built for your old profile!
There is a semi-fix, and that involves doing what a spammer might have otherwise done in your place:
- First change your username, as described above.
- Now register a new account with your old username.
- Give this new account with your old username an appropriate profile picture that clearly indicates your username has changed. See mine below:

- Put one tweet out on that new account to direct people to your new username. For emphasis, you could use that picture again.
- Add a link to your new username in the URL part and explain that this is an old username in the profile for the new account.
- Also consider following your new username (and following your old one from the new account) to highlight that it really is you and draw more attention to the new username.
- If you so wish, you can also change your background image. I didn’t bother, as I figure the profile image is enough.
Okay, I lied. Not exactly the same links, as there is no 301 redirect going on here – but it’s the next best thing.
Now you have no excuse for not changing your Twitter handle as your brand and business evolve!